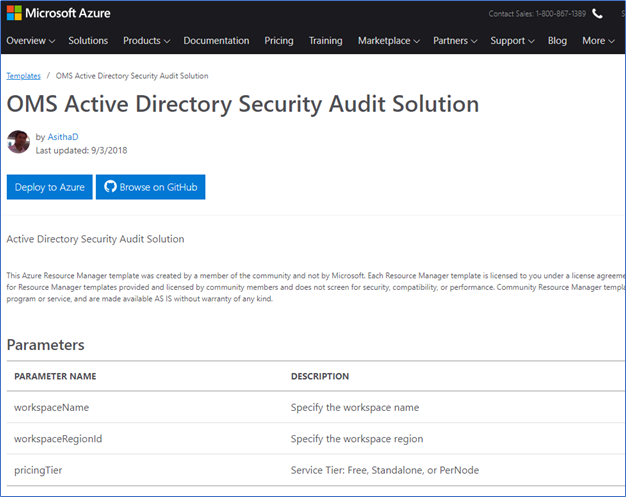
In pursuit of my previous article of Monitoring Active Directory using Operational Management Suite, I have published my own solution of OMS Active Directory Security Audit Solution to Azure QuickStart Templates. From this blog post, I’m going to give you a good understanding about the solution and how you can implement it in your Azure subscription.
Before deploying this solution, I recommend reading my previous blog post of Monitoring Active Directory using OMS. In that post, I have talked about how we can leverage OMS to monitor Active directory using Microsoft default solutions such as AD health check, AD replication solution and how we can use Azure log analytics to search and query AD security events with data. From this new solution, I have use azure log analytics quires to monitor day to day activities and critical security information where Domain Controllers logged.
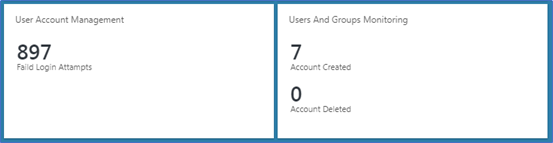
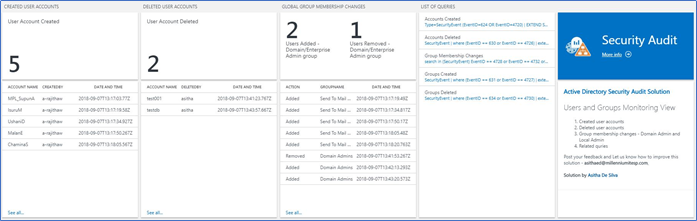
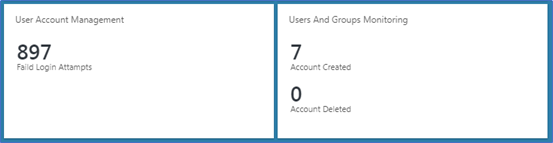
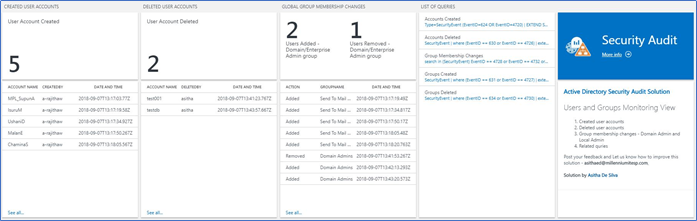
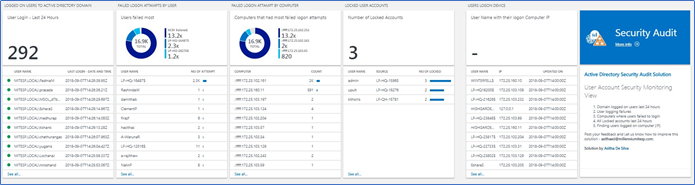
AD Security Audit Solution collects security events from domain controllers and filters them with Azure log analytics queries to visualize in OMS Dashboards. It has two attractive dashboards to display the following information.
- Created and deleted domain users with time and by whom
- Created and deleted domain groups with time and by whom
- Group membership changes with the group, added or removed user and time. (ex – Domain admin or Enterprise admin group membership changes)
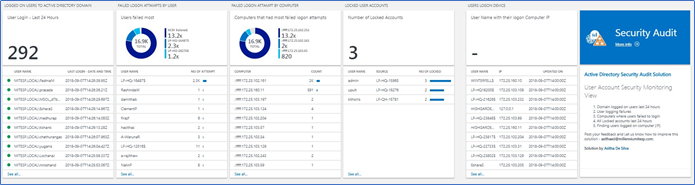
- Number of Users logged in to the domain by last 24 hours
- Domain users logged in to the domain with time and username
- Failure login attempts by the user
- Failure login attempts by computer
- Locked user accounts with the source where account locked
- Domain user logged on Computer by its IP address and the updated time and date.
Prerequisites
OMS Log Analytics Workspace
Log analytics workplace is required to host this solution. You can either select the free version or the paid version. Free version supports 500mb of daily upload and 7 days of retention.
Azure Security Center license
Azure Security Center licensing is required to collect Security events and search from Domain controllers. This is also known as OMS Security and Compliance license. Azure Security Center is offered in two tiers: Free and Standard. The Standard tier is free for the first 60 days. You can either use the free tier or use the standard node license to all domain controllers.
OMS Agent installed in Domain controllers.
OMS agent should be installed on every domain controller.
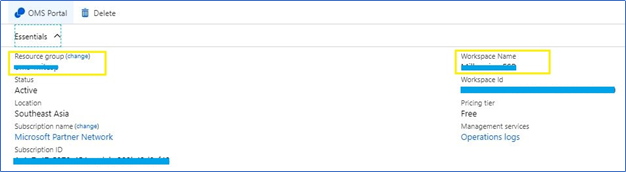
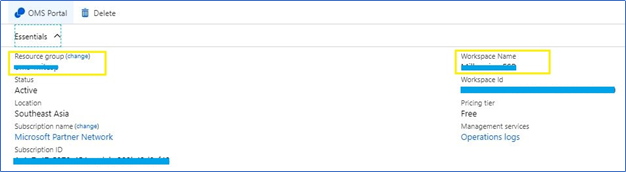
OMS workplace name and Resource group name
To deploy the solution you should know the OMS workspace name and its related resource group name, for the current version you have to deploy it to the same resource group with the workspace
Deploying the Active Directory Security Audit Solution
Follow these instructions to deploy the solution into an existing OMS workspace
- Log into Azure Portal (https://portal.azure.com) and ensure you are in the subscription containing your OMS Workspace
- Locate your existing OMS Log Analytics Workspace and note the name of the workspace, the location of the workspace, and the Resource Group
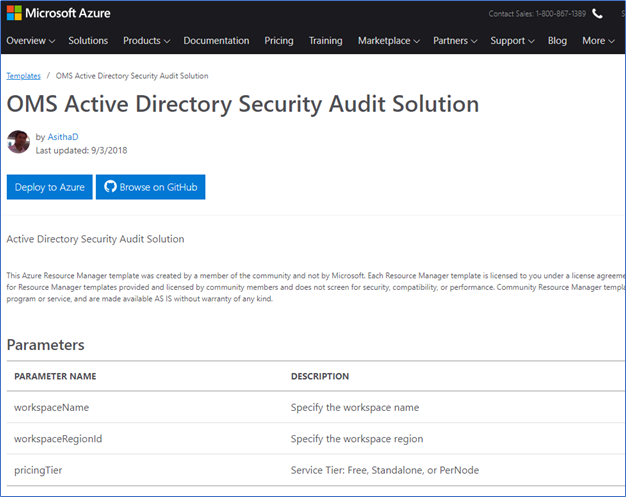
- Navigate to the following Azure QuickStart template
https://azure.microsoft.com/en-us/resources/templates/oms-active-directory-security-audit-solution/
- Click Deploy to Azure button or you can click Browse on GitHub to get more information about the solution code.
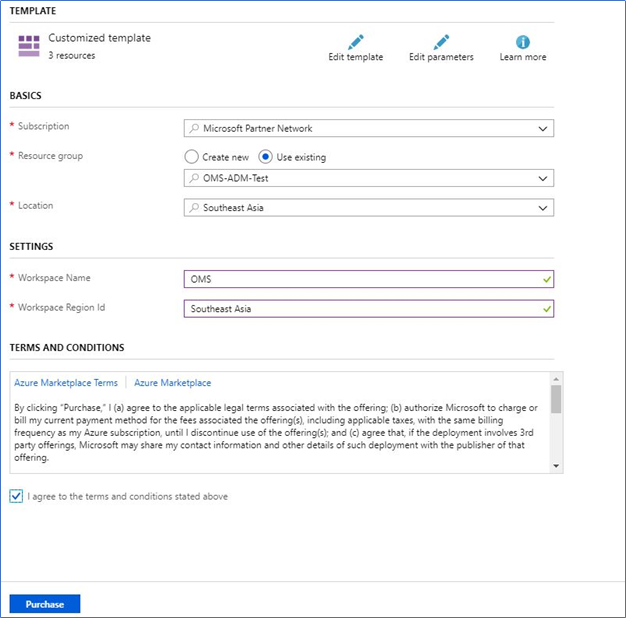
- This will send you to the Azure Portal with some default values for the template parameters. Ensure that the parameters reflect your setup so that you are deploying this into the existing Resource Group containing the Log Analytics Workspace and the Automation account.
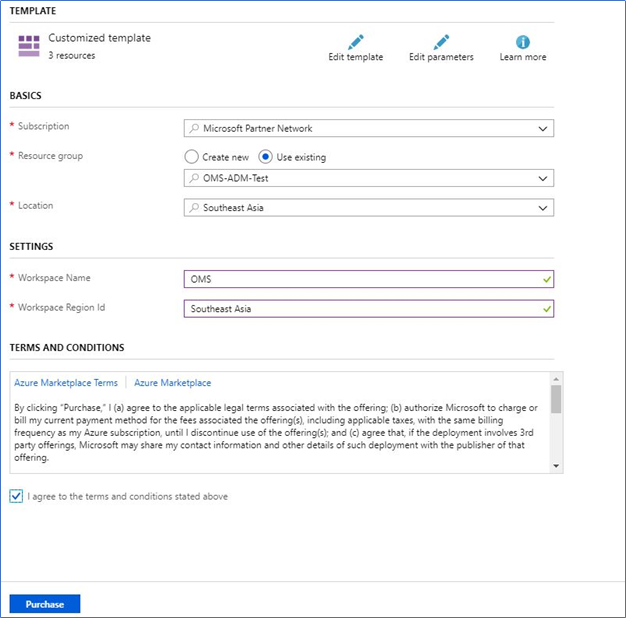
The ingestion will start 5-10 minutes post-deployment.
Note - It is important that you type the exact values for your workspace name and resource group name, and points to the regions where these resources are deployed.
Summary
If you enabled auditing on domain controllers, it will generate a fair amount of security data which you can use to search for events such as failed login or locked users. But searching this using native event viewer is not easy. OMS log analytics can be used to search these events and it will provide the information in rich presentable manner.
AD Security Audit solution is designed with the number of these important use cases most customer face day in today's business. It will help you to identify
- User’s login to the domain with a time range
- Users failed to login to the domain, incorrect password attempts, number of attempts, time where the failed attempts are made.
- Find the locked accounts. And from where the account was locked. Mainly accounts are locked by domain security policy after regularly failed attempts. But its hard to find where these attempts are made. You can use log analytics to track failed login attempts and generated IP address of those failed attempts.
- User accounts and groups created and by whom
- Any group membership changes, added to the group, removed from the group and who did this change. This is very important when domain admin group membership changes.
Hope this solution helps
Cheers
Asitha De Silva