What is Advanced Threat Analytics
ATA is an on-premise solution to help protect organizations by identifying multiple advanced attacks and inside threats. It mainly protects your Active Directory Environment and Domain controllers while scanning traffic and interesting protocols such as Kerberos, DNS, NTLM, RPC, and LDAP. Also, it can read Event logs of Domain controllers to identify threats and possible attacks.
ATA is a result of the Microsoft acquisition of an Israel startup company called Aorato in 2014. Product went private preview in 2015 and as of today it has evolved with many updated versions and the latest is 1.9. also, ATA has welcomed into the EMS, Enterprise Mobility Suite family. So if you have EMS + Security E3 licenses, you have rights to use Advanced Threat Analytics.
How ATA Works
ATA detects attacks and identifies threats using two technologies. First, it uses Behavior Analytics, ATA analysis the network traffic generating from Domain controllers and it effectively profiles your environment. ATA look at the users, computers and other entities in the environment to identify what is the normal behavior and when some abnormality is detected it will generate alerts and display detail information in the console.
Secondly, ATA can detect advanced attacks and security threats. ATA is designed to detect a number of these real attacks and with each update, it increases the detection. ATA can detect attacks such as
- Pass-the-Ticket (PtT)
- Pass-the-Hash (PtH)
- Overpass-the-Hash
- Forged PAC (MS14-068)
- Golden Ticket
- Malicious replications
- Reconnaissance
With both of those techniques, ATA can reduce the false positives of your organization and detect and show you the alerts that you really need. So with these techniques, it practically covers all of the cyber kill chains, from Reconnaissance to Lateral movement and finally to Domain dominance.
ATA Architecture
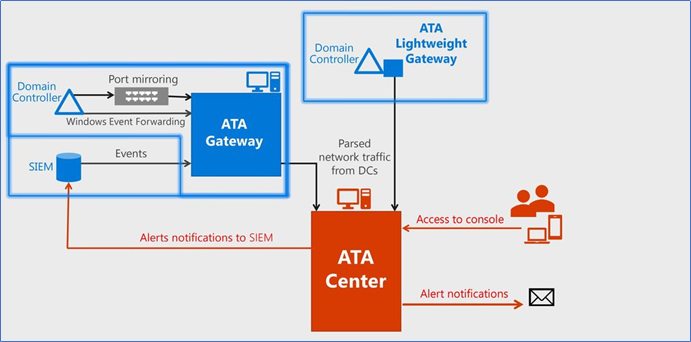
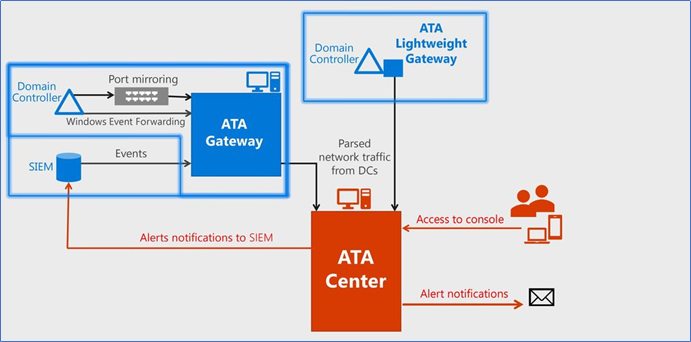
- ATA Center
The ATA Center receives data from any ATA Gateways and/or ATA Lightweight Gateways you deploy. - ATA Gateway
The ATA Gateway is installed on a dedicated server that monitors the traffic from your domain controllers using either port mirroring or a network TAP.
- ATA Lightweight Gateway
The ATA Lightweight Gateway is installed directly on your domain controllers and monitors their traffic directly, without the need for a dedicated server or configuration of port mirroring. It is an alternative to the ATA Gateway.
ATA has a rather simple architecture, it has two main components, ATA Center is where the detection happens with network traffic analyzing, protocol analyzing and profiling entities. It is where the ATA console is installed, which you can get the alerts and notifications.
ATA Gateway is the other main component. There are two gateway types, Lightweight Gateway, and the Standalone Gateway. Lightweight gateway is a service which runs directories on your domain controller, it monitors the network traffic going on and out of the domain controller, monitors the Protocols like DNS and Kerberos, also it automatically collects certain events from your domain controllers. All of these collected data are passed to the ATA Center to do the analysis.
Standalone Gateway is a gateway service running on a separate server other than a Domain Controller which it can connect to one or more domain controllers. Using port mirroring it can get the network traffic of the domain controllers. Also, here you need to configure the windows event forwarding to the standalone gateway. You can have lightweight gateways, standalone gateways or a combination of both types of gateways according to your preference.
Note – if you are using Lightweight Gateways, you need to give special considerations of the sizing. Lightweight gateway service in DC increase the resource utilization of the domain controllers, however, it monitors the utilization and if the utilization hits 85% or above, it limits the gateway service using resources. This looks good, but it has a risk, the gateway service will no longer monitor according to the fullest and you may lose some alerts in the meantime.
So it is better if you can use the sizing tool to get the current utilization and add many resources to the Domain controllers to make the lightweight gateway service run smooth.
ATA Capacity Planning
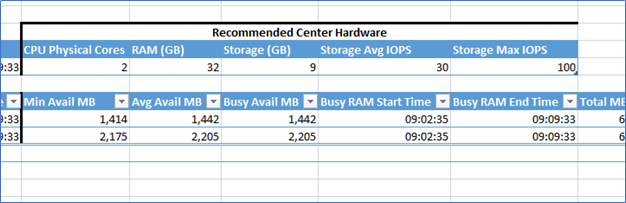
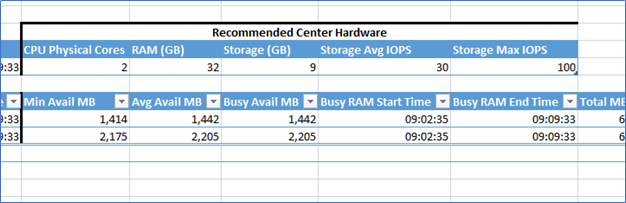
Another important topic when considering implementing ATA is the correct capacity planning. Microsoft has released a tool to do this capacity planning or in other words, sizing. ATA Sizing tool can be downloaded by clicking here and you have to install this on a domain connected machine which has access to the domain controllers. It collects packets for second information from domain controllers and Its recommend you to run this at least 24 hours. ATA Sizing tool will provide a report as an output in excel format. This sheet will provide a lot of information, however, the following information is important:
- Number of domain controllers
- Time period
- ATA Center supported or not
- Lightweight Gateway supported or not
- Max Packets/sec
- Avg Packets/sec
- Busy Packets/sec
With this information, you can refer the Microsoft TechNet sizing recommendation to select the correct capacity to your Gateway or ATA Center.
https://docs.microsoft.com/en-us/advanced-threat-analytics/ata-capacity-planning
also, the report is giving you the recommended configurations for the ATA Center as the following snapshot
Microsoft ATA is a constantly growing too with easy to manage and deploy. It has a simple architecture and does not require sophisticated hardware. ATA is a product that is continuously learning about how users, devices, and network resources behave and it is able to detect when these patterns change. With these techniques, Microsoft ATA can identify advanced persistent threats, as well as other malicious activity, better than traditional Monitoring solutions.
From this article I explained an overview about the Microsoft ATA Product, what is ATA, how it works and its architecture. From next posts, I’m hoping to discuss about deploying ATA center with ATA gateway and test some simple attacks.
Hope this post is useful
Cheers
Asitha De Silva