Windows Sandbox provides isolation of application execution, software installation, browsing and other testing limited to a temporary desktop using Windows 10 virtualization technologies. From this post, we are focusing on the use case of sandboxing and how to enable and use the feature effectively.
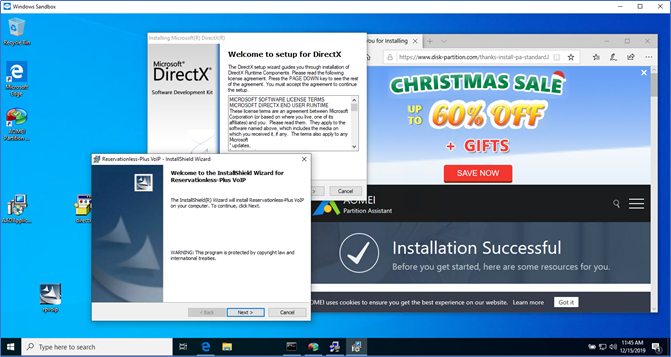
In day to day life when you are browsing the internet, you may install applications and software which you feel risky, these can be utilities and tools where you need to experiment or test something. However, the risk is massive. First, you never know what is installing and what additionally comes with the app. There can be backdoors, malware, and tools that expose your data to an intruder. And secondly, when you want to get rid of these apps, uninstallation is not easy. It might contain entries in the registry, files in the file system and some background processors.
With Windows 10 1903 Microsoft released the Windows Sandbox feature to address these problem statements. It will provide you with an isolated, temporary, desktop environment where you can run untrusted software without the fear of the lasting impact on your computer. What you run or install in Windows Sandbox stays only in the sandbox and cannot affect your host. Once Windows Sandbox is closed, all the software with its files and state are permanently deleted.
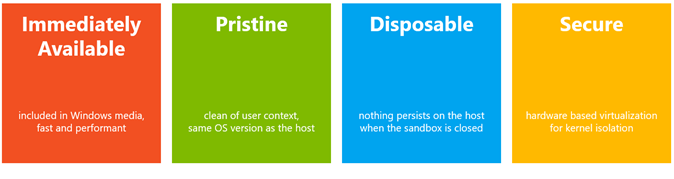
Key highlights of Windows Sandbox
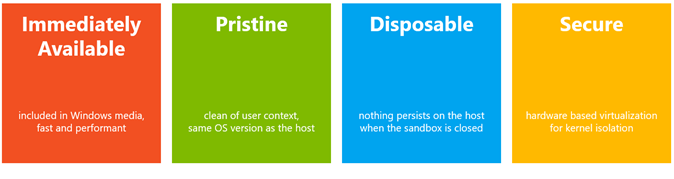
Immediately Available
Windows sandbox is available with Windows 10 Pro and Windows 10 Enterprise, there is nothing new to download or install. You just need to enable the feature from Settings.
Pristine and Disposable
Whenever the user uses the sandbox, it will be a new session. Sandbox session doesn’t have access to the host or see any content of it. It will have a clean user context and the same OS version to the host. Whatever user do in the sandbox will be flushed and refreshed after closing the sandbox session. Everything is disposable. However, if the user requires files to be copied to the host, the user can do that manually in a secured manner.
Secured
The operating system kernel is isolated from Microsoft hypervisor. The executions happen within the sandbox do not have access to the host kernel. Any exploits which targeted the kernel will contain within the sandbox and will not have any effect to the host Operating system.
Prerequisites for Windows Sandbox
- Windows 10 Pro, Enterprise or Server version
- Windows 10 1903 or Later
- Minimum 4GB Ram, 8GB recommended.
- At least 1 GB of free disk space (SSD recommended)
- At least 2 CPU cores, 64bit (4 cores with hyperthreading recommended)
- Hardware virtualization enabled from BIOS
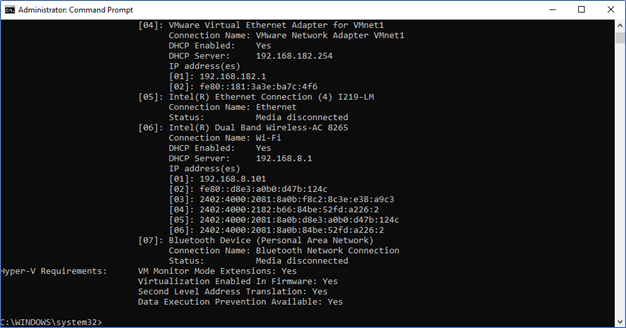
Check and enable Hardware virtualization
From Command prompt run Systeminfo.exe
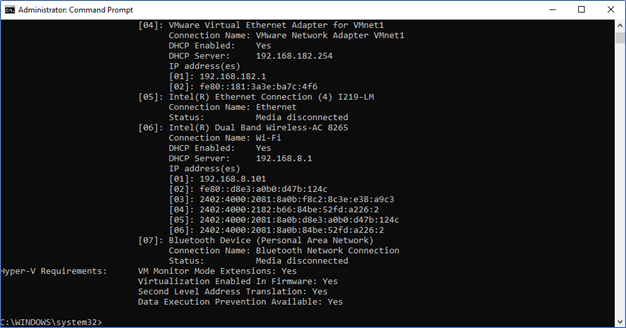
In Hyper-V requirements, Virtualization should be enabled in Firmware. If not, boot the device from BIOS or UEFI and enable the virtualization from settings, the location of this setting may vary according to your device manufacturer.
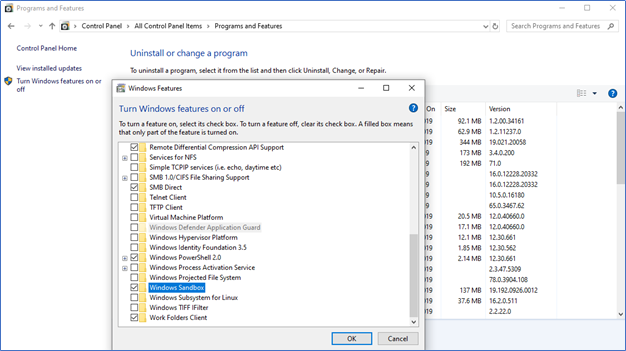
How to enable Windows Sandbox
- Open Control Panel – Program and Features – Turn Windows feature On or Off (or in Start type Turn Windows feature On or Off)
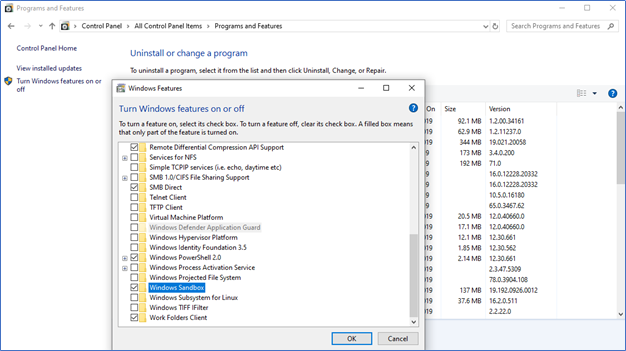
- Select Windows Sandbox and press OK
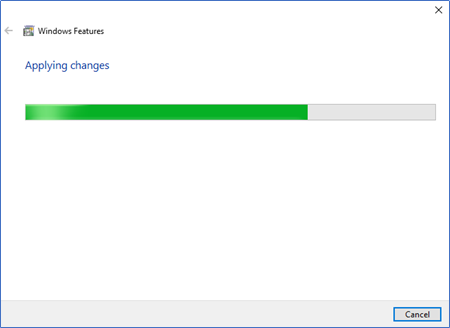
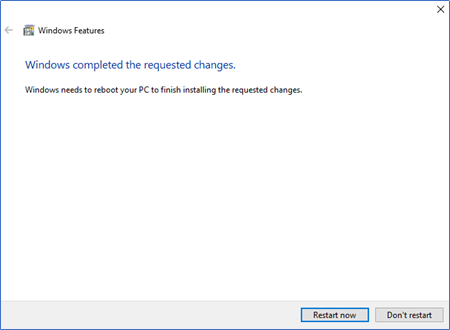
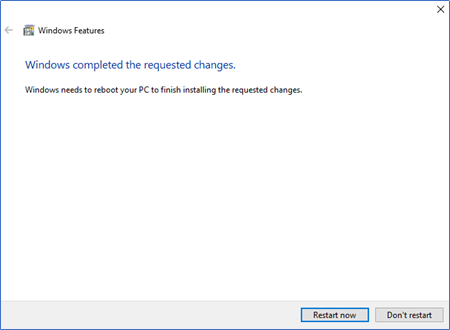
- You need to reboot the machine
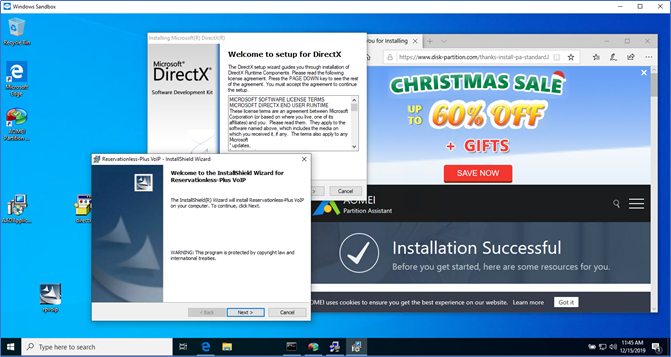
Use of Windows Sandbox
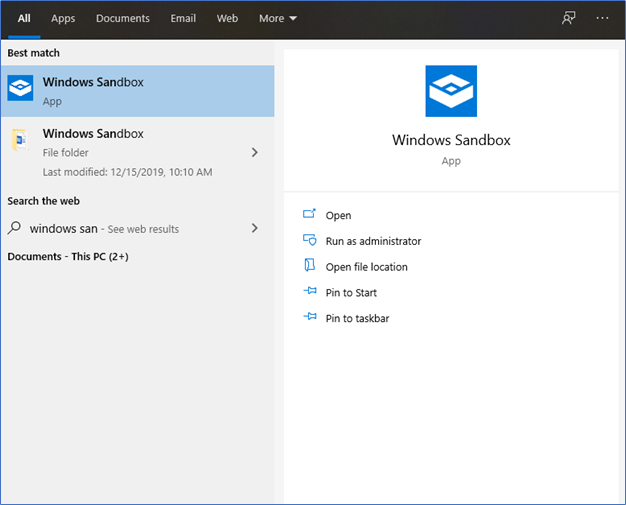
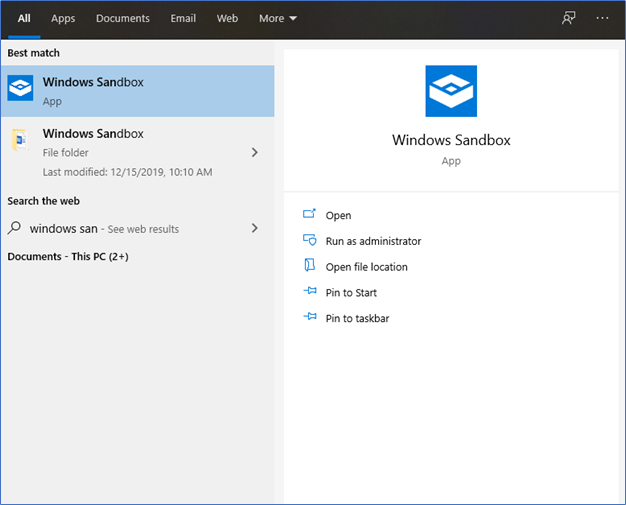
- After reboot, in Start type Windows Sandbox and Open in Run as Admin
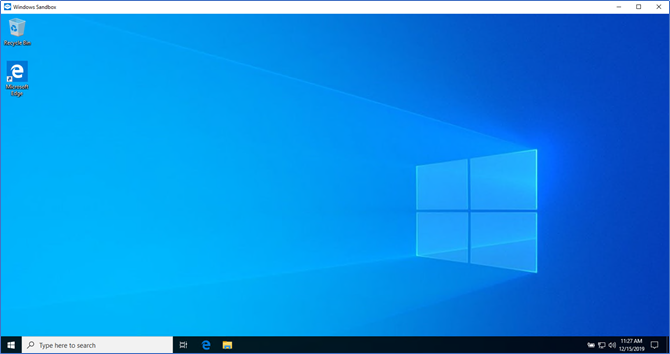
- With less than a minute a VM will spin up with all the mentioned features.
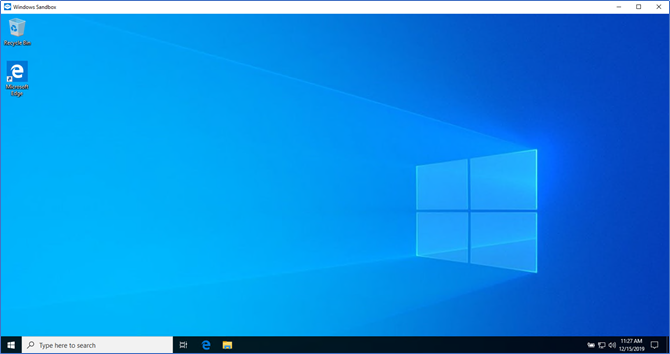
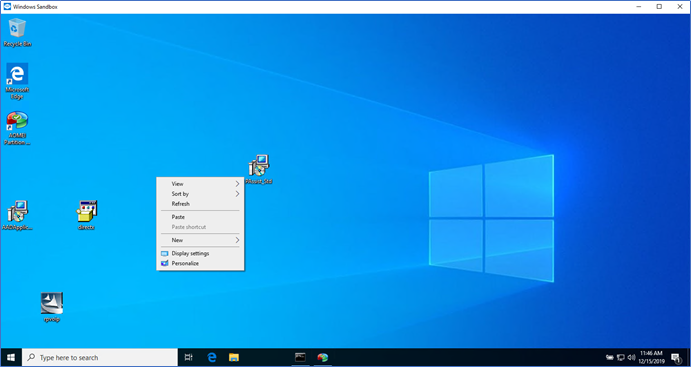
- If you want to test something from the Host, Copy and paste in the VM and run it.
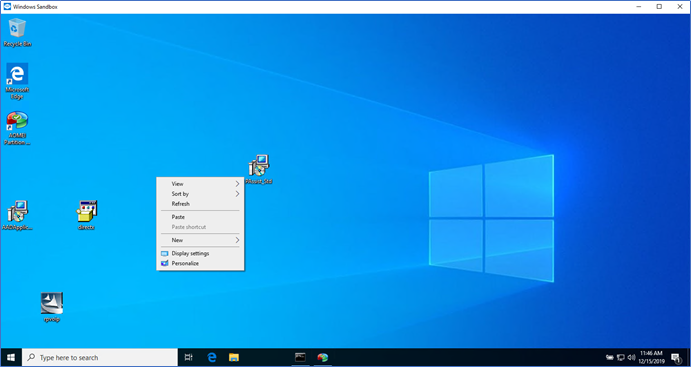
- Then you can install, run and test all these apps, without having any concerns
Windows Sandbox is continually evolving. In 2019 Ignite, Microsoft successfully demonstrates to use the Sandbox with Windows Admin center to enable and deploy apps through it. Also, they have demonstrated how to run an app in windowed mode. Where you can run and use the app from the host but it’s actually running in the Sandbox environment. Hopefully, I will try to elaborate these features from future posts with Windows Admin Center.
Hope this post is useful
Cheers
Asitha De Silva
References – Microsoft Ignite 2019, Technet