Over the time Microsoft introduced many security procedures and settings to address various security concerns and possible attacks. Introducing multifactor authentication is one of the top identity security mechanisms. Using a second factor such as SMS, Pin code or app notification reduced more than 99.9% of organization account compromise. Azure MFA has free and paid versions that can be easily integrated with WVD infrastructure. Since it is a must-have, let's see how we can integrate it with WVD and further configure it with conditional access.
Please refer my previous posts to Implement and configure Windows Virtual Desktop
01 – Working remotely and efficiently with Microsoft technologies
02 - Windows Virtual Desktop | Configuring Prerequisites and WVD Tenant Creation
03 - Windows Virtual Desktop | Create Host Pool and Access through Web, Client App and Mobile Devices
04 - Windows Virtual Desktop | Configure FSLogix User Profiles using Azure Files and AD Authentication.
05 - Windows Virtual Desktop | Manage App groups and Publish Applications
06 - Windows Virtual Desktop | 2020 ARM Version | Deployment with Domain Services
Windows Virtual Desktop relies on Azure AD for its authentications. Azure AD Multi-factor authentication comes as a free version and a paid version. The paid version comes with Azure AD Premium licenses.
Enable MFA with Azure AD free tier
You can enable the free MFA by security defaults or enabling by each user. When you apply Security defaults, MFA will enable to all users. However, this can only use with Microsoft Authenticator App. SMS and phone call verification only apply to Global administrator accounts. Let’s see how we can enable it.
Enable through Security Defaults
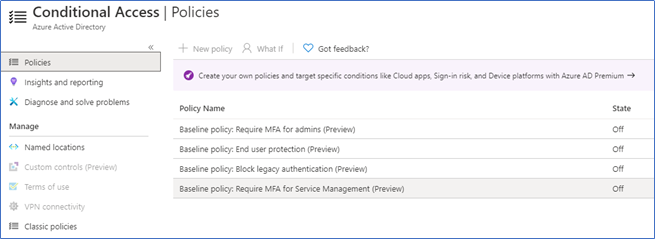
Log in to the Azure portal – Azure Active Directory – Security – Conditional access and see whether security defaults enabled.
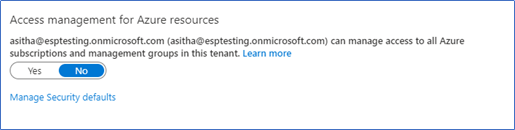
If not enabled, navigate to properties of Azure active directory, click Manage Security defaults
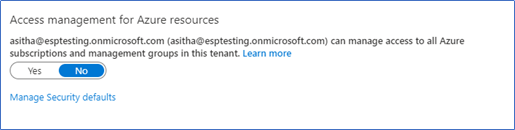
select Enable and Save

Enabling MFA by each user
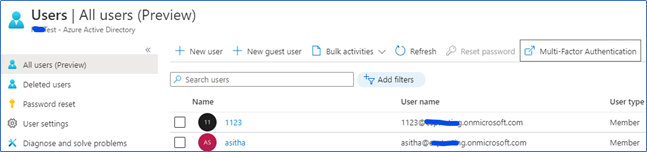
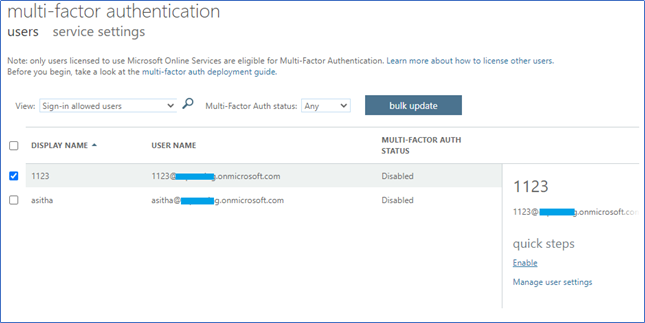
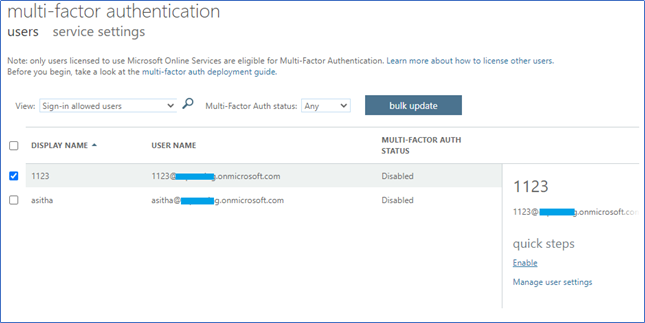
Log in to the Azure portal – Azure Active Directory – Users – Multi-factor Authentication
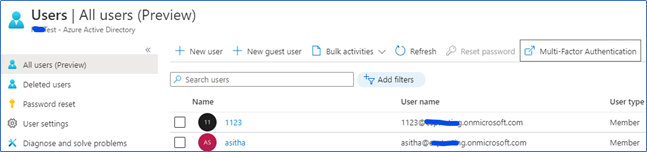
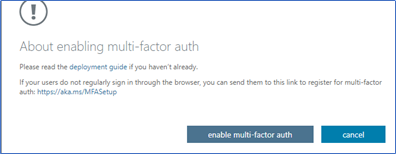
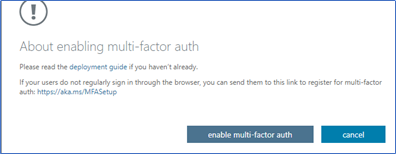
Select the relevant users in the new window, and click Enable
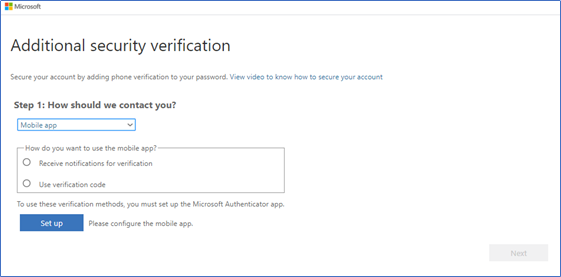
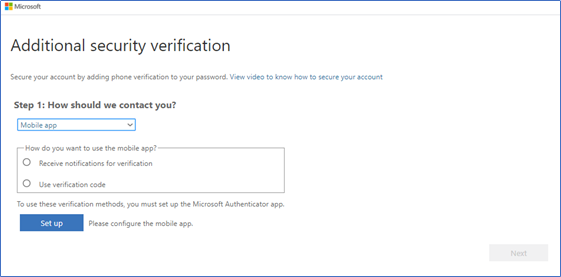
When you are login to Windows Virtual Desktop, if you are not already registered, you are required to register yourself to MFA
Enable MFA in Azure AD Licensed tier
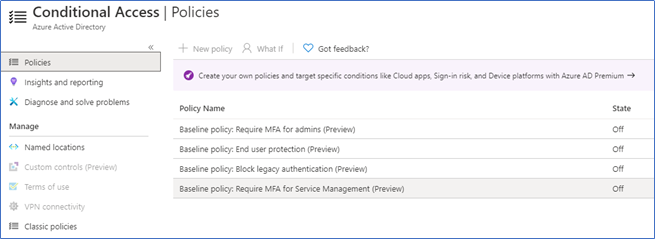
Azure MFA paid version comes with Azure AD Premium P1 and P2 plans. You can configure MFA with conditional access to further configure trusted IP ranges, selecting applications, SMS, Phone call, MFA reports, etc.
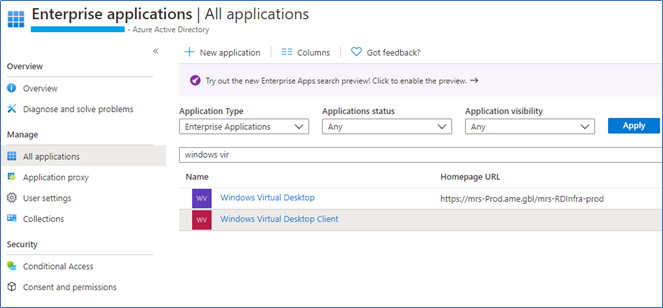
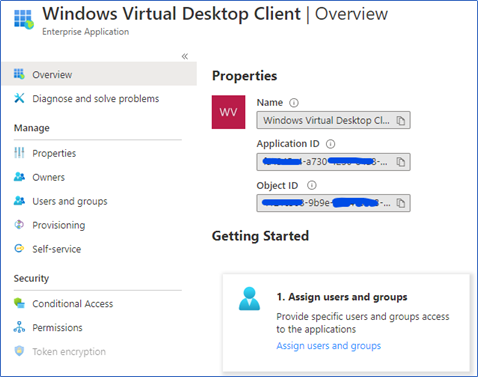
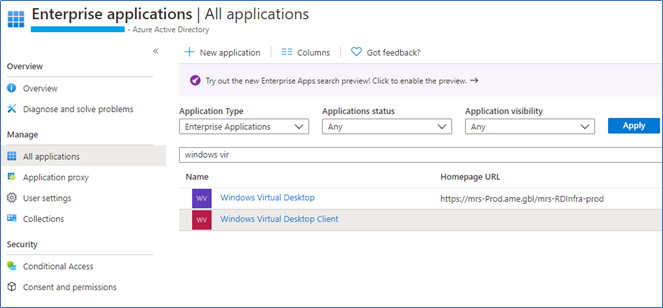
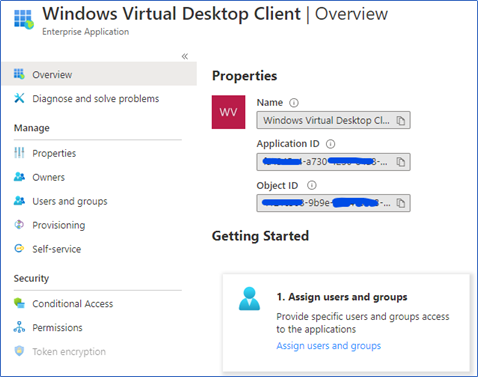
Login to Azure Portal – Azure Active Directory – Enterprise Applications and type Windows Virtual desktop on app search. Click Windows Virtual Desktop to open.
Click Conditional Access
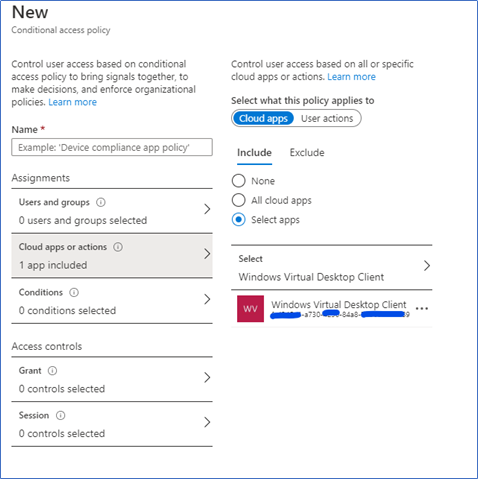
Click + New Policy to create a new conditional access policy
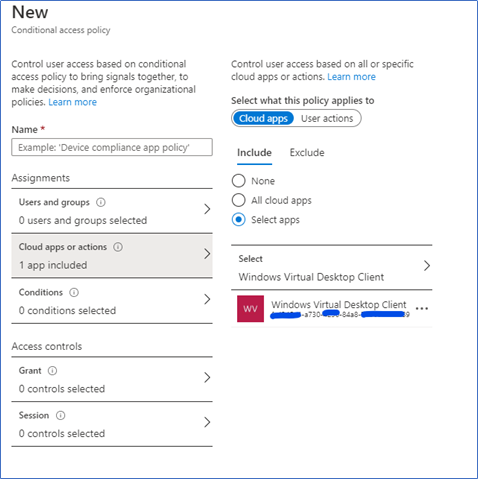
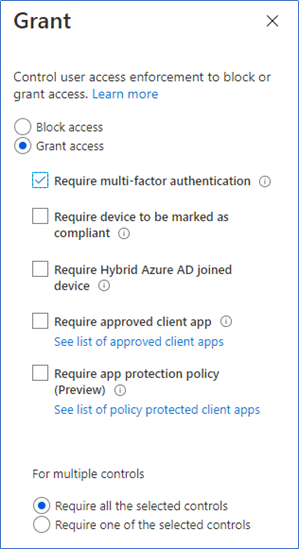
You can see the new policy already selected Windows Virtual Desktop client as the app, Name the policy, select the users, and make sure to select Require Multi-factor Authentication in Grant.
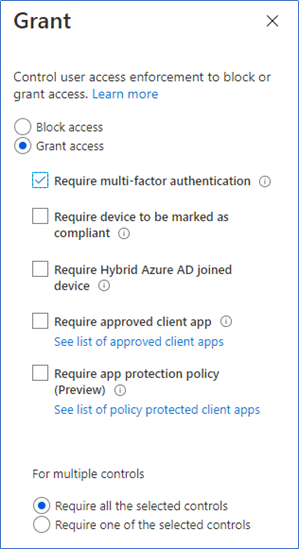
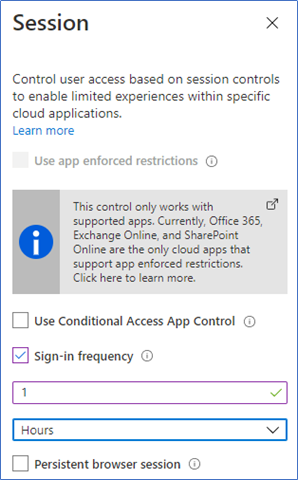
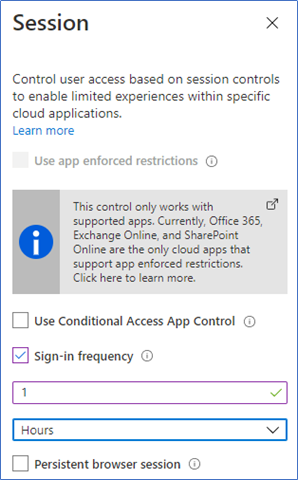
Further, you can configure Location settings and session settings. In the location you can configure include or exclude, for example, you can configure to exclude the Office network segment.
Sign in frequency is something important to WVD. When configured, disconnected, or logged off users are required to verify their second-factor authentication after the specified time. However, this will not have an impact on the active sessions.
Hope this post is useful
Cheers
Asitha De Silva