What is SAML?
Imagine, you go to a theme park and buy a ticket at the entrance for general admission. Then, every time you enter a special access area, you have to show your entrance ticket and it may be not that convenient for you. As a solution for that, theme parks now use wristbands for identification. Once you wear a wristband at the entrance, theme park staffs know that you are an authorized person. A similar technique can be adapted for the login process of web applications. Single sign-on (SSO) authentication allows users to enter their login credentials for one time and then, they are able to access multiple applications and services without entering their usernames and passwords over and over again. Google’s G Suite is one of the best examples of the use of SSO authentication. G Suite consists of applications including Gmail, Calendar, Drive, Maps, and Docs, etc., and once the users are logged in, they could access all the G Suite applications without re-entering them. How is this possible and what are the technologies behind that? SAML is the underlying technology that makes possible the SSO authentication.
Security Assertion Markup Language (SAML) is an XML-based open-standard and basically is designed to accomplish authentication and authorization between the Identity Provider (IdP) and the Service Provider (SP) or applications.
Authentication – Challenges the users to validate the login credentials (username/password, two-factor authentication, etc.) and determines who they claim to be.
Authorization – After successful authentication, authorization determines the permissions and access levels of applications for users.
By adopting the SSO authentication framework, SAML allows the login credentials of a user to be shared across multiple applications and services which results in the fast and easy login process and also strengthens the security as well. As SAML is based on the XML, it is considered as a flexible standard and XML uses to transfer authentication and authorization data securely between the Identity Provider and Service Provider. After authenticates the users’ identity, SAML authorizes them to access the application resources according to the granted access levels.
SAML was developed in 2001 by the Security Service Technical Committee (SSTC) of Organization for the Advancement of Structured Information Standards (OASIS) and in November 2002, OASIS had launched the first version of SAML (SAML v1.0). In March 2005, OASIS had published their newest version (SAML v2.0) by replacing SAML v1.1 and it still functions as the current version of the SAML standard. SAML also accepted as building blocks of Federated Identity Management (FIM). When implementing Business to Business (B2B) and Business to Customer (B2C) single sign-on systems, organizations often make use of SAML for an effective and secure SSO solution.
SAML Providers
SAML Providers are responsible for performing the authentication and the authorization processes on users in order to access the applications they want. There are two SAML providers to perform these tasks.
Service Providers (SP)
Service Providers are applications and services which usually users want to access. Service providers do not involve in to authenticate the users. Therefore, to access the service providers, users are required to go through a proper authentication process with the Identity providers. Before the SSO authentication, applications and services had to maintain their own databases to store the user credentials and users were able to directly access these resources. But, they had to remember the credentials for each and every application.
Identity Providers (IdP)
Identity providers are responsible to store the login credentials of users and perform the authentication process in order to verify the users who they claim to be and send what users are authorized to access to service providers.
SAML Assertion
A SAML Assertion is an XML document that sends by the identity provider to the service provider. It contains all the information that requires the service provider to decide to grant permissions for the user. SAML specifies three types of assertion statements namely authentication statements, attribute statements, and authorization decision statements. An authentication statement contains the proven identity of the user and time and the method of authentication. The attribute statement provides specific information about the user. Authorization decision statement indicates that access permission to the application has been granted or not.
How SAML works
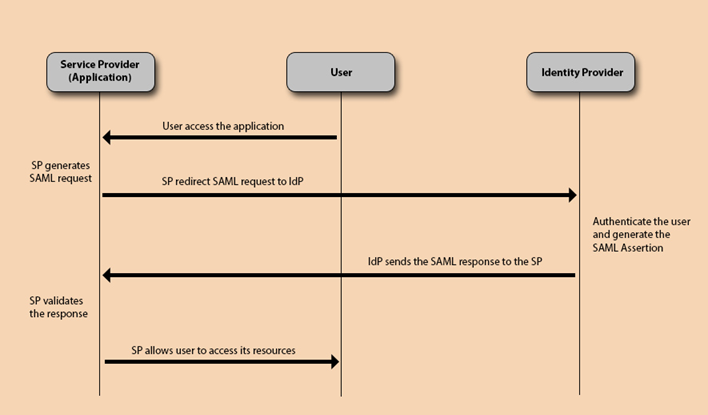
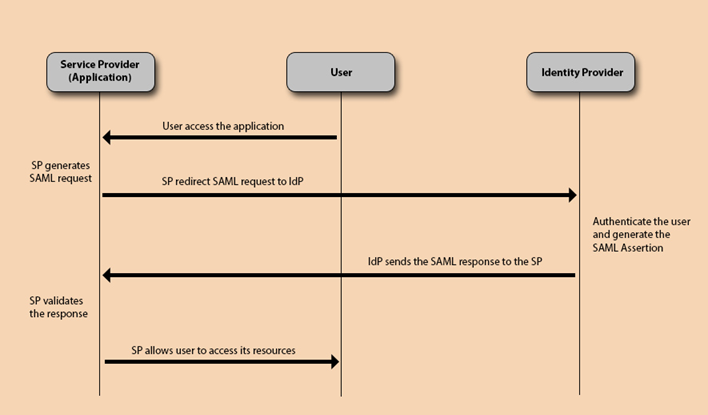
Suppose a user operates in an SSO environment and that user is trying to access a particular web-based application. A typical authentication process with SAML is proceeding like this;
- First, the user attempts to access the Service Provider (application) by clicking a link or by directly typing the URL on the browser.
- Then, the Service Provider generates a SAML request and redirects the user to the Identity Provider.
- If the user is already authenticated, permissions will be granted immediately. Otherwise, the Identity Provider launches the authentication process.
- After that, Identity Provider will generate the XML-based SAML Assertion and sends back to the Service Provider.
- The Service Provider validates this response and allows users to access its resources.
Benefits of SAML
- Users don’t need to keep multiple usernames and passwords to log in to their web accounts, because SSO authentication requires only to maintain a single set of login credentials for all the web applications. This will improve the user experience through quick and secure access to applications.
- Before the SAML, Service Providers required to maintain the users’ account information in their own databases. SAML transfers all these account information to the Identity Providers. This will reduce the administrative costs for Service Providers.
- SAML has standardized its format by enabling interoperate with any system independent of implementation. Which means SAML supports the platform neutrality.