Working from home is now practical, more efficient, and cost-effective for organizations. It is the new normal. To make it a reality, IT has to make a few changes to its existing systems and policies. They might have to buy new solutions, modifying the current network setup, introduce new security policies, and perhaps they have to ignore some current security practices. However, device compliance is something that cannot ignore. From this post, I'm discussing a permanent solution to make your current System Center Configuration Manager available at all times, whether the users connecting from the Internet or Intranet.
SCCM is available for internet clients from its older releases such as SCCM 2007. However, it heavily depends on the PKI certification-based infrastructure. Even with the Cloud Management Gateway release, clients still have to rely on a Certificate that should be trusted by the CMG and the SCCM Management point. This is not practical for total work from home scenario because deploying certificates and managing it will be a headache to IT, with users totally connecting from the internet.
Microsoft Introduced Token-Based Authentication for Cloud Management gateway with the Release of SCCM 2002, which is now also known as MECM Microsoft Endpoint Configuration Manager 2002. Since our hot topic is token-based authentication, let's discuss that before moving to CMG.
What is Token Based Authentication
Token-based authentication, which was released with Configuration Manager 2002, helps users to connect to CMG without a client authentication certificate. When the client registers with The management point, it gives the client a unique token that shows it's using a self-signed certificate. When the client roams onto the internet, to communicate with the CMG, it pairs its self-signed certificate with the management point-issued token. This will overcome following limitations and configuration challenges when configuring CMG
- The need for a client authentication certificate
- Deploying client authentication certificate to Internet-connected machine
- Challenges when deploying SCCM Agent to Internet-connected devices
- No need to join devices to Azure Active Directory or enable Co-Management
Further to these challenges, Token based authentication is easy to configure and less troublesome if you configure it correctly. To fully utilize this scenario, you need to upgrade the SCCM site server to the 2002 or above version. Also, all the clients should be upgraded to the latest. After the upgrade, token-based authentication can be workable with the following two methods.
Internal Network Registration
From this method, clients will get the Token automatically from the site server management point. The client should be connected to the internal network; token registration will happen on client installation or restarting the SMS Agent Host service restart.
Internet – Bulk Registration
This method is to install the SCCM client through the public internet. You need to generate the bulk registration token from the site server and copy it to the internet-facing client device and run it with CCM setup files. With this token client will contact the CMG and register itself with the management point. A bulk registration token is a token with a short validity period. It allows the client to generate a unique token, which, paired with its self-signed certificate, lets it authenticate with the CMG.
When the SCCM agent successfully initiates a connection with management point through CMG, these unique Token will renew itself once a month, a token has a validity of 90 days, and it can connect to the CMG to renew its token. However, if the client couldn't connect to the CMG for 90 days, it is required to connect to the internal network to renew the Token.
What is Cloud Management Gateway
Cloud Management Gateway enables clients to connect to the site server management point through the public internet. It is a hosted cloud service in Azure. Using CMG organization can avoid exposing on-premises infrastructure to the internet.
CMG helps work from home devices to connect to the configuration manager site server without connecting to the intranet from VPN; your devices can be online from the public internet. It will help to deploy software updates, applications, compliance, hardware-software inventory, and other configuration manager features. Not only public-facing devices, but CMG also enables workgroup devices and DMZ connected devices to connect to the configuration manager environment.
Supported Configurations Manager Features
Following features are supported when clients connecting from CMG
- Software distribution
- Hardware and software inventory
- Software updates
- Endpoint protection
- Compliance settings
- CMPivot
- Client status and notifications
- Run scripts
- Client install – with Token authentication or AAD Integration
- Windows 10 in-place upgrade task sequence
- Task sequence without a boot image, deployed with the option to Download all content locally before starting task sequence
- Task sequence with a boot image started from Software Center
Prerequisites of CMG with Token-based authentication
- Azure Subscription to host the CMG - CMG require an Azure tenant to host its cloud services, this will include least 1 VM according to your sizing.
- Azure Subscription admin rights required (global admin)
- SCCM 2002 or above – site servers and clients should be upgraded to 2002 or above version
- Unique CMG DNS Name – Unique DNS name, which should represent in the server authentication certificate.
- Server Authentication Certificate
A server authentication certificate required when configuring CMG from the configuration manager site server. It will enable secure communication with the Configuration manager, and Azure-hosted CMG through Internet. Also, CMG connecting clients should trust this certificate to allow communication. Server authentication certificate can be a Public certificate or certificate issued from your internal Public Key Infrastructure (PKI) / Enterprise certificate authority. If it's from your internal PKI, your clients should have a trusted root certificate.
- Registration of classic computer resource provider from Azure subscription
- Network port requirement
With CMG, you don't need to worry about opening any network ports to your on-premises network. The service connection point and CMG connection point initiate all communication with Azure and the CMG. Outbound network connectivity is described in this article (Here).
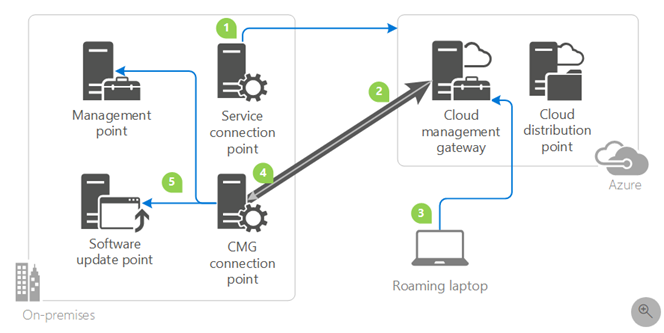
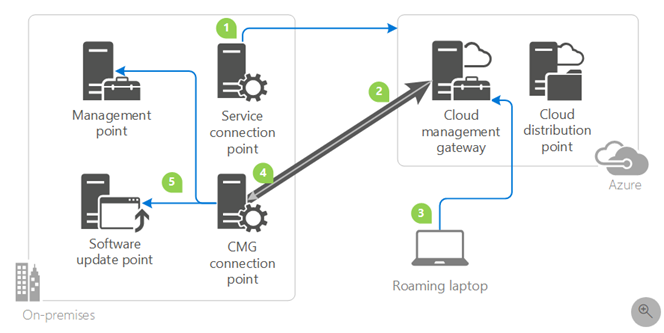
Below network diagram represents the connection flow.
Sizing / Costing Estimation
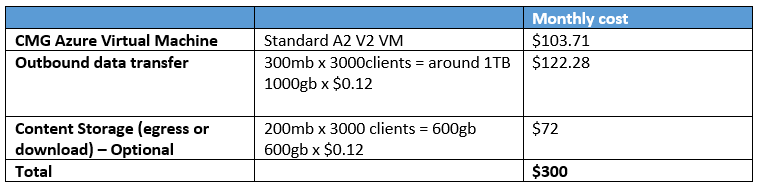
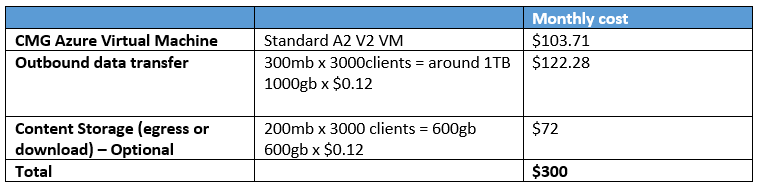
When planning for CMG, you can do a rough estimation of Azure costs; however, it will always be an estimation because this may vary according to the usage of CMG. The following elements contribute to the CMG monthly costs.
Number of Virtual Machines
CMG cloud service uses Azure VM's to host its services; as of today, it uses A2 V2 per instance. As per the Microsoft recommendation, 1 CMG instance will support up to 6000 simultaneous connections. However, to maintain HA, you have to put 2 CMG instances, which means two A2V2 VM's. This can configure when you are installing the CMG.
Content Storage
This cost is to store, download and upload applications, packages, and other content you need to deploy to users. Software updates should not upload into the cloud DP because they can configure to deploy from Microsoft Update services.
Outbound data transfer (egress or download)
These are the traffic flow from CMG to clients and CMG to the site server. These can be policy retrieval, applications, and packages to clients. And reports client information transfer from CMG to the site server. This costing is difficult to estimate; it will depend on your application deployments, policy retrieval intervals, and a number of clients connecting from CMG. However, data transfer costs are very low in Azure.
By considering these cost factors, I have assumed and estimate costs for 3000 clients in the following table.
From the next post, I'm discussing step by step in implementing Cloud Management Gateway with Token-based authentication. Stay tuned 😊
Hope this post is useful
Cheers
Asitha De Silva