The Cybercrime Economy
Cybersecurity challenges are escalating at an alarming pace, making it extremely difficult for organizations to manage the growing threat landscape. Today’s headlines highlight the impact of ransomware, espionage, and the weaponization of cyber in modern warfare. These reports clearly show the increasing sophistication within the underground cybercrime economy. Each day, cybercriminals execute highly targeted, sophisticated attacks against organizations and individuals, exploiting weaknesses across systems, networks, and devices. Ransomware, in particular, has evolved into a gig economy.
The cybercrime economy, along with the speed, scale, and sophistication of attacks, is expanding exponentially. Password-related attacks have increased tenfold, rising from 3 billion to 30 billion in the same period. Beyond the surge in attacks, the pool of attackers is also growing rapidly. Microsoft is now monitoring more than 300 major threat actors across financial crime and nation-state operations, up from 200 just a year ago. The impact of these attacks can be devastating.
To make matters worse, organizations face unprecedented layers of complexity. On average, enterprises rely on 80 distinct security tools and are expected to integrate them to ensure data and insights flow seamlessly while maintaining effective operations. Meanwhile, the global workforce is struggling, with 3.4 million security jobs currently unfilled. With AI adoption accelerating, nearly one in three business leaders is concerned about data loss from improper AI use. At present, the odds are heavily stacked against defenders.
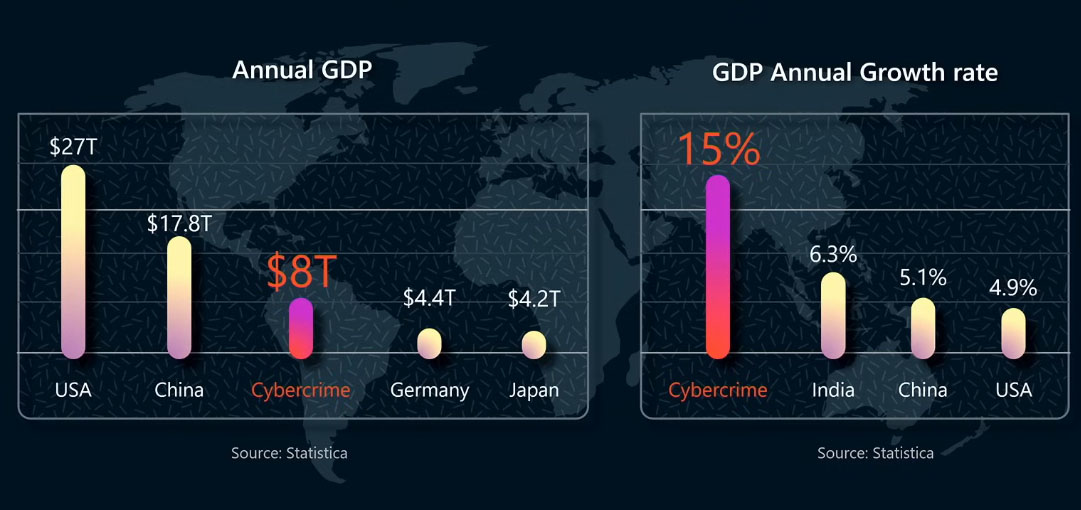
Globally, the cost of the cybercrime economy is projected to surpass 8 trillion US dollars. To put that into perspective, if the global GDP losses from cybercrime were treated as a standalone economy, it would rank third globally, behind only the United States and China. Even more concerning, the cybercrime economy is expanding far faster than the fastest-growing economy in the top 20, India.
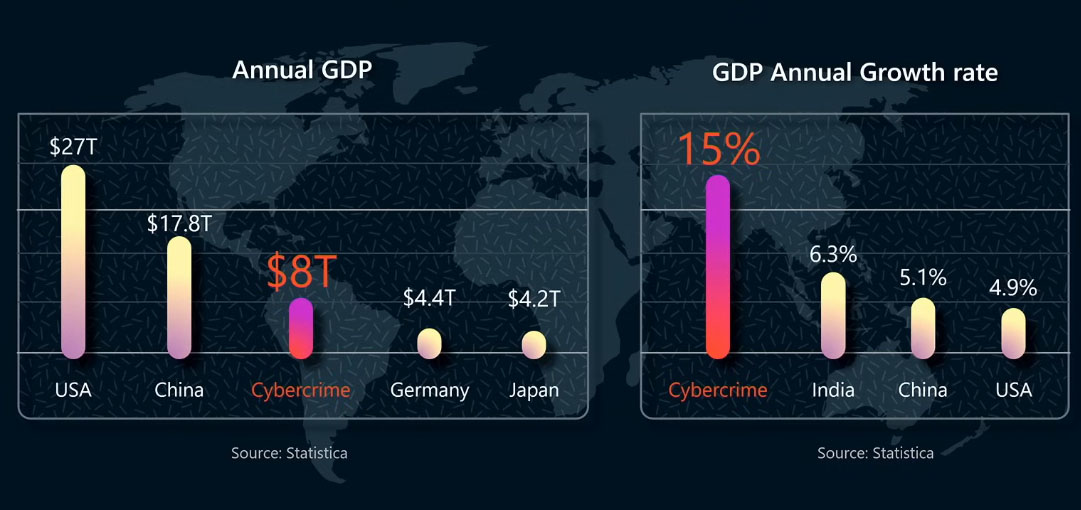
Cybercrime has effectively become both the world’s third-largest economy and the fastest-growing one. The speed, scale, and sophistication of these attacks, combined with a significant talent shortage and the operational complexity organizations face, are giving attackers a clear asymmetric advantage over defenders. Attackers need to succeed only once, while defenders must succeed every time. It is no surprise that cybersecurity has become one of the most urgent challenges of our era, requiring a fundamental paradigm shift.
The Microsoft Advantage: A Security Flywheel
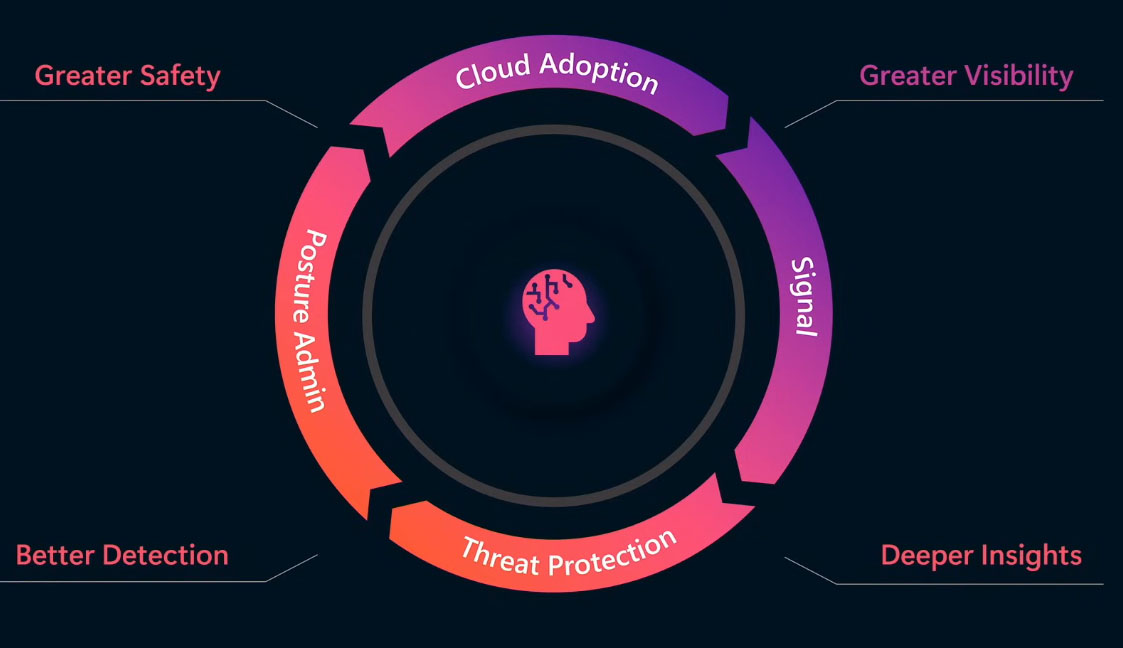
Microsoft is leading this transformation. It combines three unique advantages found nowhere else: large-scale data and threat intelligence, the most complete end-to-end protection, and industry-leading responsible AI. Together, these advantages fuel a powerful flywheel of innovation. As security becomes more connected through the cloud, enhanced visibility accelerates the signal processing within the flywheel, generating insights that enable stronger threat protection. Improved protection leads to more accurate detections, providing deeper insight into proactive measures to strengthen the security posture. This results in greater safety, which in turn drives broader cloud adoption. The flywheel has been in motion for some time, but with AI at the core, it is now spinning at machine speed.
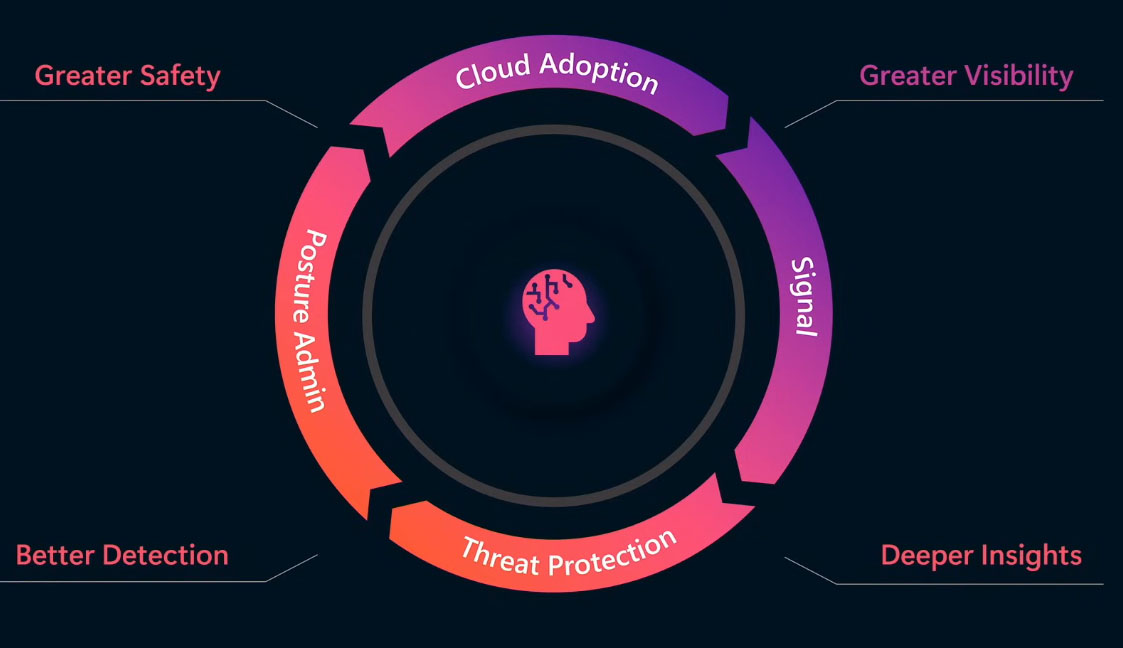
Consider each section of the flywheel and its three core advantages. Signals are critical because protection is impossible without visibility. Microsoft’s security delivers a large-scale data advantage by processing 65 trillion signals every day. This provides a clear understanding of attacker activities and enables stronger defenses against evolving threats. When combined with global threat intelligence expertise and insights into attack behaviors drawn from more than a million customers and over 15,000 partners, this capability becomes even more powerful.
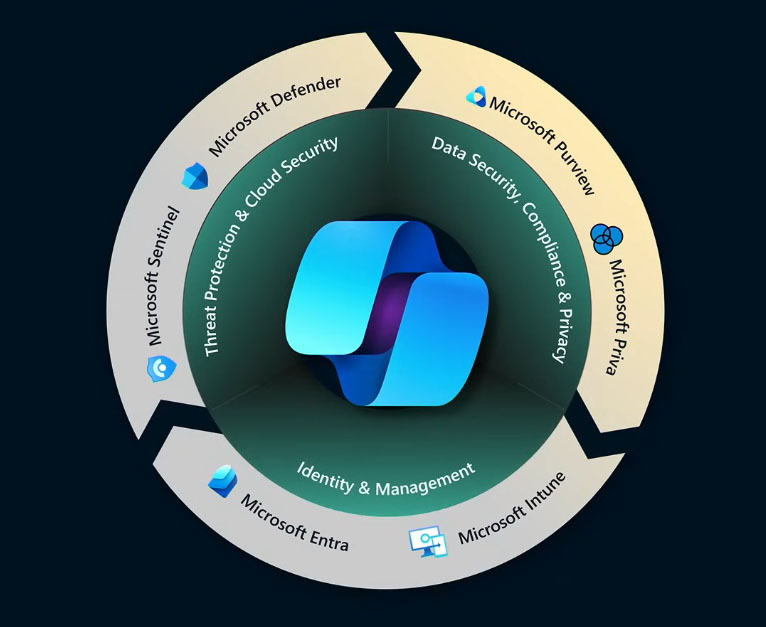
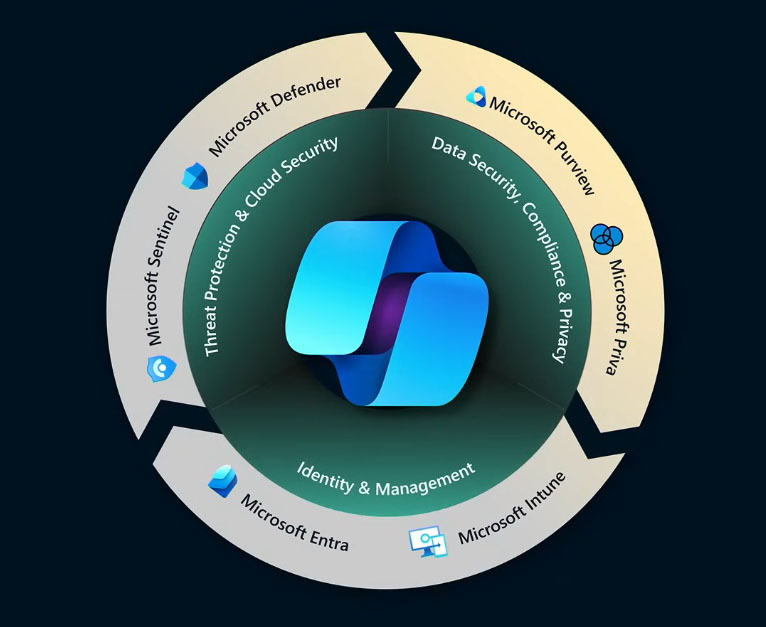
The next section of the flywheel is end-to-end protection. Safeguarding a digital estate requires securing every layer, including data, identities, applications, cloud, and infrastructure. Microsoft security protects from every angle, unifying security, compliance, identity, management, and privacy across 50 categories within the Microsoft Security Cloud, which is composed of six product families. Microsoft Defender and Microsoft Sentinel deliver threat protection and cloud security. Microsoft Purview and Microsoft Priva address data security, compliance, and privacy. Microsoft Entra and Microsoft Intune provide identity and access management. Together, these solutions form a protection flywheel in which each element reinforces the others.
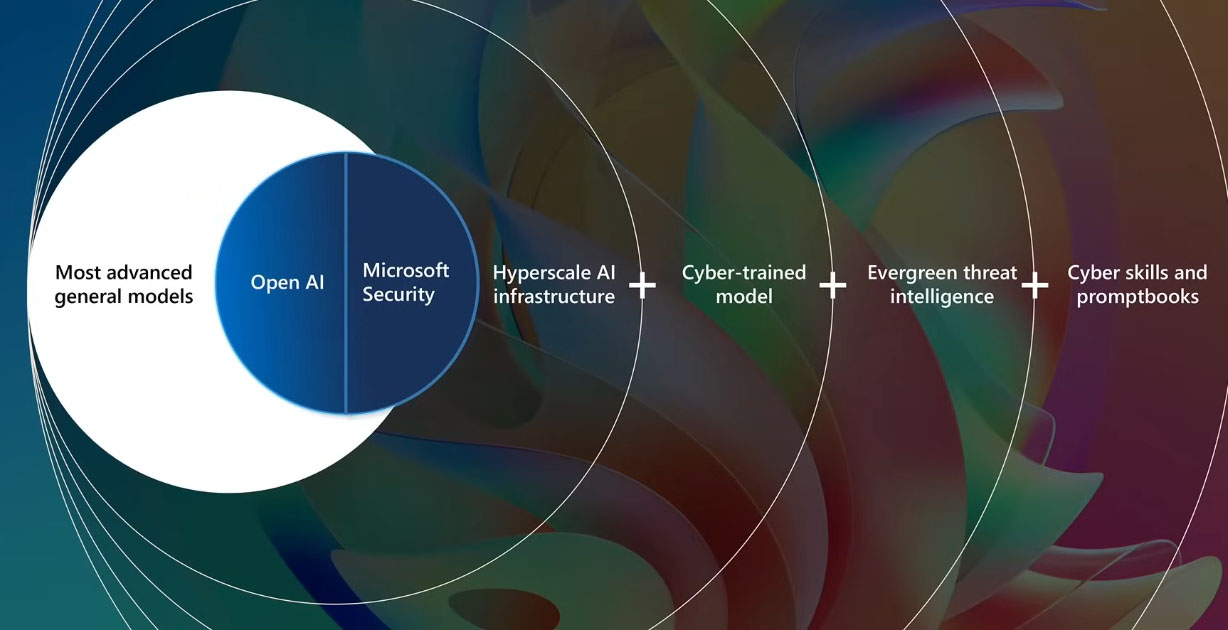
Microsoft has made significant progress in end-to-end protection. But with generative AI, a major leap forward is now possible. AI can harness the full scope of signals and resources with expertise that surpasses what any individual could achieve. Microsoft has long been committed to AI and is recognized as a leader in delivering generative AI to organizations worldwide. The company understands the full technology stack, from building AI applications to operating them securely and at scale. You may encounter plenty of hype from legacy security vendors claiming AI enhancements to their current products, which in most cases will amount to simple chat applications. Microsoft Security Copilot goes far beyond this. It begins with the most advanced OpenAI model, GPT-4, which will continue to evolve, and layers on a Microsoft-developed, security-specific model, continuously updated threat intelligence, a growing library of cyber skills, and promptbooks, all powered by Microsoft’s secure and trusted AI infrastructure.
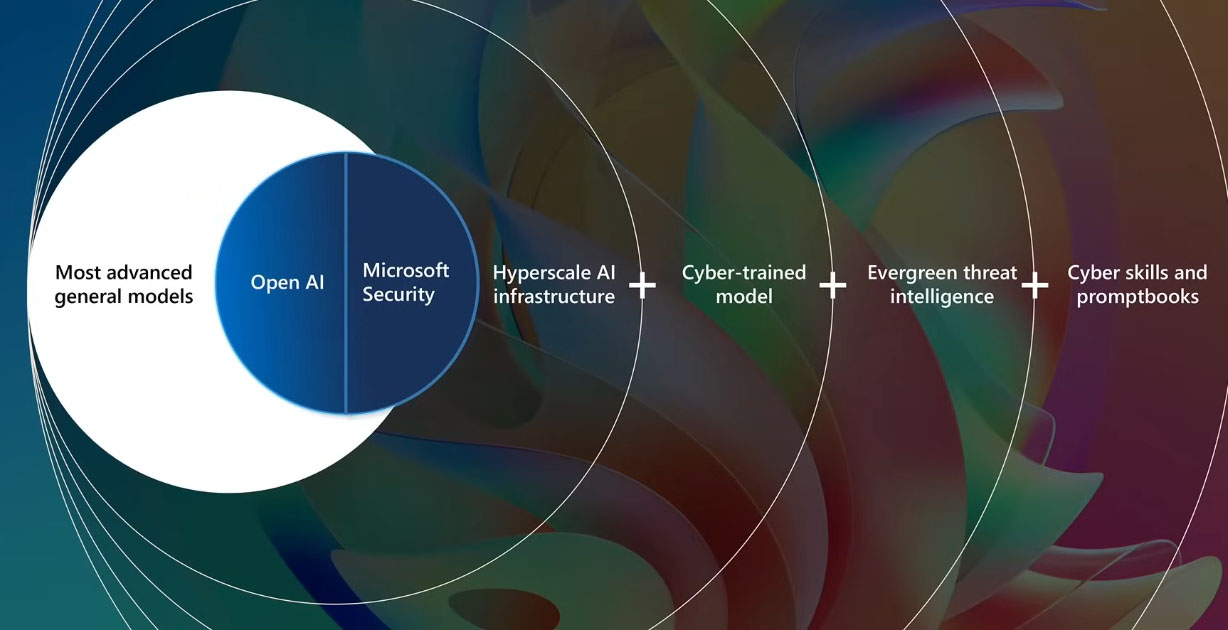
In general, chat applications process a request by sending a single call to a large language model, known as an inference. Typically, one request equals one inference. In security, handling the volume and complexity of data often requires a dozen or more inferences to ensure responses are accurate and well-grounded. Microsoft Security Copilot goes beyond simply summarizing a prompt. It reasons across multiple data sources, performing at machine speed what would otherwise take a human hours to complete.
Microsoft Security Copilot
Microsoft Security Copilot is the first generative AI security product built on the latest GPT-4 models to protect organizations at machine speed and scale. It constantly learns from Microsoft’s global threat intelligence, security data, and skill usage to provide tailored insights that strengthen defenses and accelerate response. With Microsoft Security Copilot, natural-language questions can quickly clarify what is happening in an environment. It can answer a wide range of security-related queries, from identifying which incidents require attention to assessing their impact on the organization and, most importantly, determining the actions to take. It then provides clear recommendations for next steps.
Microsoft’s security teams face attacks every day, defending both customers and the company itself. This experience led Microsoft to create Security Copilot, which helps IT and security professionals enhance their skills, improve team collaboration, and detect attacks that often go undetected due to fragmented security tools or staffing shortages. These challenges are critical to overcome, and Microsoft is rapidly innovating to integrate Copilot across all security and compliance solutions while expanding end-to-end capabilities to ensure organizations have the strongest possible protection.
To demonstrate how Microsoft empowers each critical role within its comprehensive security approach, consider a common phishing email many have encountered. A single click can trigger serious compromises, ranging from identity theft to malware infections to network breaches. Once a user is compromised, attackers may gain access to sensitive customer or financial data. Each suspicious action, such as clicking a phishing link, triggers a wave of alerts for the security operations team, who often must sort through hundreds of alerts daily. This constant overload makes it easier for stealthy threats to evade detection. The challenge is compounded by alerts spread across multiple disconnected tools, spanning identity and access management, email security, endpoint management, cloud security, and more. For decades, security operations teams have faced the burden of managing these siloed systems.
In recent years, the growth of advanced threats has driven the adoption of Extended Detection and Response (XDR) to consolidate critical signals. Alongside this, Security Information and Event Management (SIEM) solutions aggregate signals from diverse sources and play essential roles. In many organizations, XDR and SIEM serve as the primary tools for security operations teams. But what if they could be unified? Microsoft has combined its XDR solution, Microsoft Defender, and its SIEM solution, Microsoft Sentinel, to create the industry’s first unified security operations platform. This shift streamlines the industry, moving from fragmented tools to a single unified platform that eliminates silos and integrates Microsoft Security Copilot capabilities. As a result, defenders gain a generative AI companion designed with deep, security-specific expertise. At the same time, IT admins use Microsoft Entra, the multi-cloud identity and access solution, to protect identities and ensure secure access to any resource. Because complexity can escalate quickly, Microsoft Copilot is embedded within Entra to simplify and accelerate critical tasks.
There is another potential consequence of a phishing campaign. Consider what happens without attack disruption, if the attack continues, and stolen credentials are used to access customer data. At that point, a data loss investigation is required. Every employee in the organization needs access to data, yet that data is often scattered across multiple environments. For many organizations, this includes multiple clouds, making investigations extremely complex. To address this, Microsoft Copilot is being embedded in Microsoft Purview, the data security and compliance solution, making it easier than ever to protect critical data.
Reference:
Microsoft Events